BYOD, CYOD, COPE, COBO, COSU – zrozumieć i zbudować strategię zarządzania urządzeniami mobilnymi
Co oznaczają?
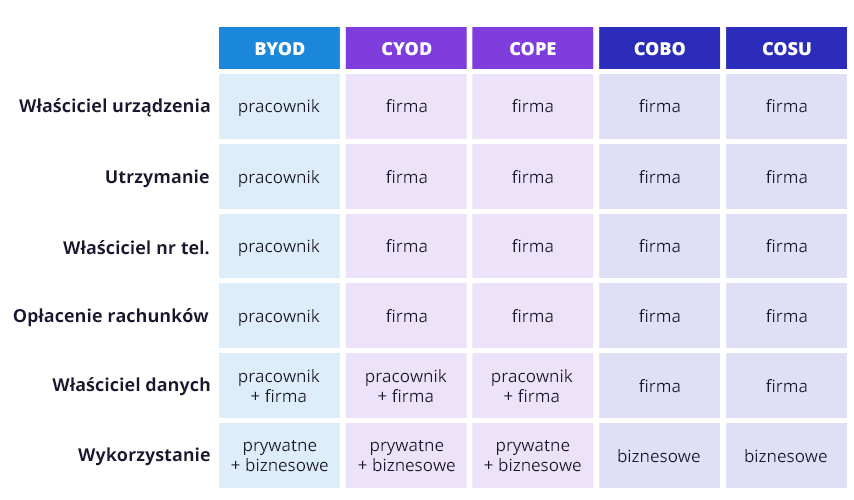
BYOD, CYOD, COPE, COBO oraz COSU to akronimy opisujące polityki stosowane wobec urządzeń mobilnych, używanych w organizacji. Inaczej zwane są także modelami zarządzania mobilnością organizacji. Najprostszym kryterium ich podziału jest własność.
Urządzenia możemy zatem podzielić na urządzenia prywatne, stosowane w modelu:
- BYOD – Bring Your Own Device – przynieś swoje własne urządzenie;
oraz urządzenia będące własnością firmy (COD – Company Own Devices), używane w modelach:
- CYOD – Choose Your Own Device – wybierz swoje urządzenie;
- COPE – Corporate Owned, Personally Enabled – własność firmy, udostępniona do użytku prywatnego;
- COBO – Corporate Owned, Business Only – własność firmy, tylko do użytku biznesowego;
- COSU – Corporate Owned, Single Use – własność firmy, ograniczona do określonego celu biznesowego.
Jak to intepretować?
Właściciel urządzenia ponosi koszt jego zakupu oraz utrzymania. Ma także możliwość wyboru kupowanego urządzenia. Jedynym nagięciem tej reguły jest model CYOD, w którym firma daje pracownikowi możliwość wyboru urządzenia ze zdefiniowanej przez siebie listy.
Z własnością urządzenia ściśle powiązana jest własność numeru telefonu i karty SIM, używanej na danym nośniku. Nie praktykuje się rozdzielania tych dwóch aspektów. W związku z tym właściciel urządzenia ponosi także koszty usług telekomunikacyjnych.
Kolejnym elementem, w kontekście własności, jest własność danych przetwarzanych na urządzeniu, co jest powiązane z charakterem jego wykorzystania. Modele BYOD, CYOD oraz COPE przewidują jednoczesne używanie urządzenia do celów prywatnych i biznesowych. Rodzi to wiele obaw związanych z zabezpieczeniem danych, ich administrowaniem, czy też przenikaniem się strefy służbowej i prywatnej.
Jak stworzyć własną politykę?
Warto zacząć od potrzeb. Opisane wyżej modele powinny stanowić drogowskaz, a nie sztywne ramy, w które trzeba się wpasować. Wybierając lub tworząc politykę zarządzania mobilnością, warto zacząć od weryfikacji pięciu najważniejszych obszarów:
- Urządzenie: kto je wybiera, kto płaci za jego zakup, kto jest jego właścicielem, kto jest odpowiedzialny za jego utrzymanie oraz kto jest właścicielem danych na nim zawartych – jaki charakter wykorzystania urządzenia przewidujemy.
- Usługi: kto jest właścicielem numeru karty SIM, kto opłaca bieżące rachunki za korzystanie z usług telekomunikacyjnych – w tym też roaming wynikający np. z podróży służbowych.
- Zarządzanie i wsparcie: kto zarządza urządzeniem i kto jest odpowiedzialny za wsparcie. Tutaj warto pamiętać, że jedynie instalacja agenta MDM/UEM umożliwia zdalne zarządzanie urządzeniem, a tym samym pozwala na zapewnienie pełnego wsparcia.
- Integracja i aplikacje: jaki poziom integracji ze środowiskiem firmowym jest wymagany do zachowania odpowiedniego workflow. Każda szersza integracja, poza podstawowymi narzędziami typu poczta czy wideokonferencje, wymaga większych nakładów pracy przy wdrożeniu oraz zarządzaniu.
- Oczekiwania vs. rzeczywistość: jaki dział zajmie się wdrożeniem i obsługą stworzonej polityki, czy czas potrzebny na jej realizację zmieści się w czasie pracy obecnych pracowników, czy posiadamy odpowiednie narzędzia/systemy do zarządzania.
Czy da się spełnić wszystkie oczekiwania?
W bardziej rozbudowanej strukturze może to być trudne. Rozwiązaniem jest zachowanie balansu pomiędzy poziomem kontroli a elastycznością wdrożenia polityki/modelu. Największy poziom kontroli uzyskasz w modelu COBO i COSU, później COPE i CYOD, a na samym końcu BYOD. Natomiast najłatwiej wdrożyć model BYOD, bo od razu z przyjściem pracownika do firmy, posiada on urządzenie, którym będzie mógł się posługiwać w ramach operacji biznesowych.
Nie trzeba wybierać tylko jednego typu urządzeń czy modelu zarządzania. Polityki mogą się zmieniać w zależności od działu, urządzenia czy też obszaru działań. Bez względu na wybrany kierunek, stworzenie konkretnych zasad pozwala na świadomą ochronę organizacji i pracowników. Wdrożenie narzędzia do zarządzania urządzeniami może ułatwić zadbanie o bezpieczeństwo, zgodność z przepisami prawnymi i utrzymanie oczekiwanego poziomu wydajności. W modelach, które łączą przestrzeń służbową i prywatną może okazać się wręcz niezbędne.
Profesjonalny system MDM/UEM pozwoli nie tylko na utworzenie takiej przestrzeni, zarzadzanie jej bezpieczeństwem, ale także usunięcie czy skasowanie danych w sytuacjach tego wymagających.
Chwyć trochę wiedzy z Proget – sprawdź inne nasze artykuły:
- Cyberhigiena w biznesie – poznaj proste zasady i dowiedz się, jak możesz ją wspierać
 Cyberbezpieczeństwo to istotny element zaufania zarówno do organizacji, jak i w jej obrębie. Szczególnie w… Czytaj więcej: Cyber hygiene in business – learn the simple rules and how you can support it
Cyberbezpieczeństwo to istotny element zaufania zarówno do organizacji, jak i w jej obrębie. Szczególnie w… Czytaj więcej: Cyber hygiene in business – learn the simple rules and how you can support it - Dlaczego warto wybrać producenta, który posiada certyfikat ISO 27001?
 Czym jest norma oraz certyfikacja ISO 27001? Norma ISO/IEC 27001 jest międzynarodowym standardem dotyczącym zarządzania bezpieczeństwem informacji [...]… Czytaj więcej: Why choose a vendor that is ISO 27001 certified?
Czym jest norma oraz certyfikacja ISO 27001? Norma ISO/IEC 27001 jest międzynarodowym standardem dotyczącym zarządzania bezpieczeństwem informacji [...]… Czytaj więcej: Why choose a vendor that is ISO 27001 certified?
